This site uses cookies. By continuing to browse the site you are agreeing to our use of cookies.
All
Bitcoin Magazine
Web3 is going just great
Crypto Briefing
Coinjournal
Cryptocurrency| Finance Magnates
Bitcoinist.net
Bitcoin
Bitcoin News
Cointelegraph.com News
CoinDesk
The potential future of the U.S. and Global e...
Apr 4, 2025 0
The potential future of the U.S. and Global e...
Apr 4, 2025 0
Cheapest way to invest in BTC?
Apr 4, 2025 0
All
GeekWireGeekWire
The Information
Mashable
Futurism
Techradar - All the latest technology news
Top News - MIT Technology Review
VentureBeat
The Register
The Hacker News
Digital Trends
CNET News.com
The Next Web
Gizmodo
Slashdot
TechCrunch
WIRED
The Verge - All Posts
Engadget
Ars Technica
Nyan Heroes trailer reveals launch window and...
Apr 3, 2025 0
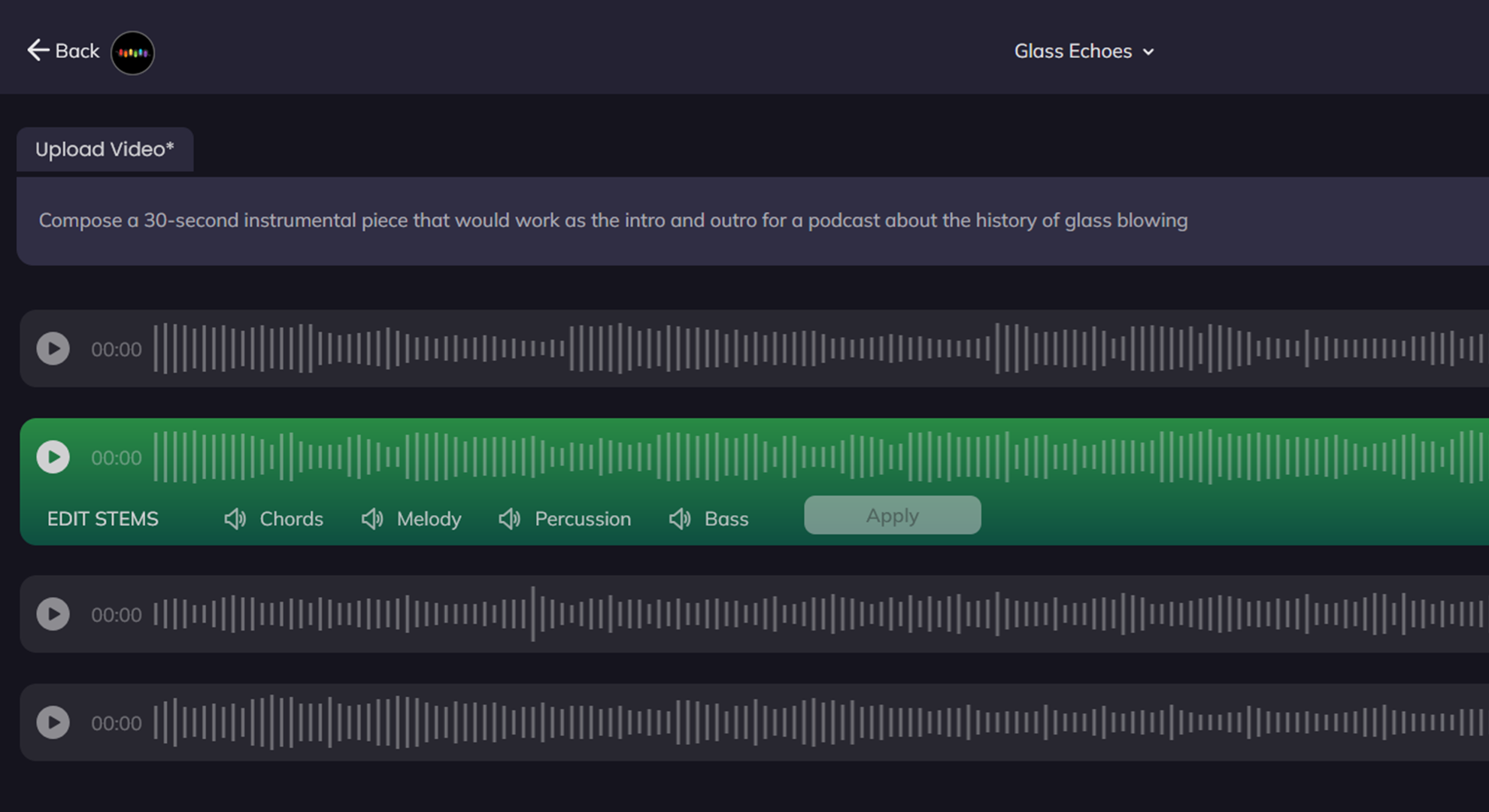
The tool integration problem that’s holding b...
Apr 2, 2025 0