How the hybrid work boom reshapes corporate security
It is vital that companies have cyber threat protocols in place with cyber attacks constantly on the rise and evolving to make recovery as hard as possible.

In the aftermath of the COVID-19 pandemic the UK has witnessed a seismic shift in work patterns, with a staggering 41% of workers now engaging in remote work. This trend towards hybrid work arrangements has been on a consistent and steep rise, introducing major cybersecurity concerns for organizations around the world.
As companies adapt to this new reality, they face the multifaceted challenge of managing unsecured networks at home, coupled with a lack of IT oversight and insufficient employee awareness.
A paradigm shift
The transition to hybrid work models has been swift and widespread, marking a paradigm shift in how businesses operate. What began as a necessary response to lockdown measures has evolved into a preferred mode of working for many employees and employers alike. It’s not just working from home which is an issue, employees can often work abroad in other countries.
This change in usual business dynamics offers numerous benefits, including improved work-life balance, reduced commuting times, and potential cost savings for businesses. However, it also brings with it a host of cybersecurity challenges that organizations must address urgently to ensure their long-term viability and security.
The weakest link
Many employees work on home Wi-Fi networks that lack enterprise-grade security measures - making them vulnerable to attacks. These networks often use default or weak passwords, outdated firmware, and may not have proper encryption protocols in place. This creates an easy entry point for cybercriminals to intercept sensitive data or gain unauthorized access to corporate systems.
Blurring the lines between work and personal
The use of personal devices for work purposes, often referred to as ‘Bring Your Own Device’ (BYOD), can lead to data breaches if these devices are not properly secured or managed. Personal devices may lack the latest security patches, have outdated antivirus software, or contain malicious applications that could compromise corporate data.
Limited IT oversight
Remote work environments make it challenging for IT teams to monitor and manage security effectively, potentially leaving vulnerabilities unaddressed. The inability to physically access devices or networks complicates troubleshooting and security enforcement, leading to potential gaps in the organization's security posture.
The human factor
Without proper training, employees may inadvertently expose company data or fall victim to phishing attacks and other social engineering tactics. The human factor remains one of the most significant vulnerabilities in any security system, and the distributed nature of hybrid work exacerbates this risk.
Employees working remotely may resort to using unauthorized applications or services to facilitate their work, a practice known as shadow IT. This can introduce unknown vulnerabilities into the corporate network and make it difficult for IT departments to maintain control over data flow and security.
Cloud security risks
The increased reliance on cloud services for collaboration and data storage introduces new security challenges that must be carefully managed. While cloud services offer flexibility and scalability, they also present new attack vectors if not properly configured and secured.
Building a resilient defense
As hybrid work becomes the norm, companies must critically address their security systems to protect against evolving cyber threats. It is vital that organizations have comprehensive cyber threat protocols in place, especially considering that cyber attacks are constantly on the rise and evolving to make recovery as difficult as possible.
Key steps that companies should consider include:
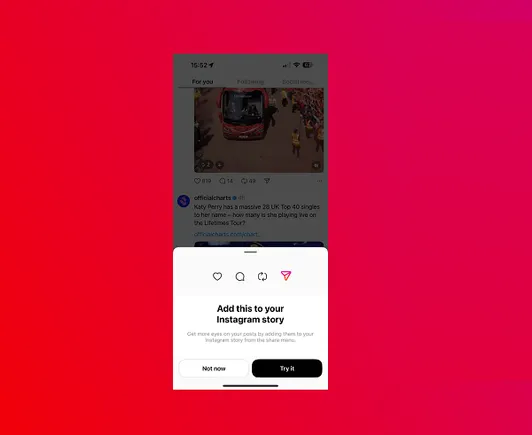
Implementing multi-factor authentication (MFA): MFA adds an extra layer of security to prevent unauthorized access to company systems and data. By requiring multiple forms of verification, such as a password combined with a fingerprint or a one-time code sent to a mobile device, MFA significantly reduces the risk of unauthorized access even if credentials are compromised.
Deploying virtual private networks (VPNs): VPNs create secure connections for remote workers, encrypting data in transit and protecting against eavesdropping. This is particularly crucial when employees are using public Wi-Fi networks or working from locations with potentially compromised internet connections.
Enhancing endpoint security: Robust protection for all devices accessing company resources is crucial in a distributed work environment. This includes implementing and regularly updating antivirus software, firewalls, and intrusion detection systems on all endpoints, including mobile devices and laptops.
Adopting cloud-based security solutions: Cloud-based security solutions can provide scalable and flexible security measures that adapt to the needs of a hybrid workforce. These solutions often include features such as real-time threat detection, automated patch management, and centralized security policy enforcement across all devices and locations.
Conducting regular security training: Ongoing cybersecurity awareness programs for all employees are essential to mitigate human error-related risks. This training should cover topics such as identifying phishing attempts, proper handling of sensitive data, and best practices for secure remote work.
Implementing Zero Trust architecture: A Zero Trust security model assumes that no user or device should be automatically trusted, regardless of their location or network connection. This approach requires continuous verification and authorization for all access requests, significantly reducing the risk of unauthorized access.
Staying ahead of the curve
The shift to hybrid working has necessitated significant investments in technology and resources. However, it has also presented an opportunity for businesses to modernize their security posture and build resilience against emerging threats. Companies that successfully adapt to these changes can not only protect their assets but also gain a competitive advantage in attracting and retaining talent.
Beyond implementing technical solutions, organizations should focus on fostering a culture of security awareness among their employees. This involves regular communication about security best practices, recognition of employees who demonstrate good security habits, and integration of security considerations into all aspects of business operations.
We rate the best business VPN.
This article was produced as part of TechRadarPro's Expert Insights channel where we feature the best and brightest minds in the technology industry today. The views expressed here are those of the author and are not necessarily those of TechRadarPro or Future plc. If you are interested in contributing find out more here: https://www.techradar.com/news/submit-your-story-to-techradar-pro




![Experts Don’t Believe AI Tools Will Lead to Mass Job Losses [Infographic]](https://imgproxy.divecdn.com/gcXE1_Da13Oz-JAszjUwb6v5UqMp2MFMjDAIXPbLad0/g:ce/rs:fit:770:435/Z3M6Ly9kaXZlc2l0ZS1zdG9yYWdlL2RpdmVpbWFnZS9haV9qb2JfbG9zc2VzLnBuZw==.webp)